Brent Benner is founder and president of Canopii Collaborative.

Tell me about yourself and the company.
I was born and raised in Texas up until about high school, then spent several years in the Midwest and Texas. I spent two years as a Peace Corps volunteer in Peru. I got back the day before Thanksgiving in 2008, when the stock market dropped like 500 points and launched the financial crisis. I had studied finance and entrepreneurship in school, but finance was definitely not going to be a good path at that moment. I worked at Microsoft for a while, but I was looking for something more purpose-driven like I had done in Peace Corps.
I was seeking jobs only in Austin and Chicago when Epic called me. I figured that a practice interview would be good, and I had heard good things about Madison. Epic just blew me away, so I took that job and ended up staying there for eight years. I started on the implementation team for Tapestry, which is part of the payer suite. I pretty quickly moved into director of product management for the payer suite and acted as the primary liaison between our clients and the software engineering team to help formulate the roadmap.
Ultimately, I couldn’t deal with those cold winters of Wisconsin anymore, so I returned to Texas and launched Canopii in 2021. While I was at Epic, it was pretty clear to me that a lot of firms provided Epic consulting services, but no one was hyper-focused on the payers. We launched Canopii to do just that, to provide purpose-built consulting for health plans and managed care organizations.
That intentional focus has led to a lot of growth. We started with four consultants in 2021, and now we have about 70, of whom 60 focus specifically on the Epic payer suite.
Epic’s payer suite is made up of a couple of products, with Tapestry and Payer Platform being the flagships. Those are used by health plans, essentially the insurance companies or the payer side of the business, rather than the provider side, although we work with a lot of provider-sponsored health plans that work in an integrated environment between the health system and the health plan.
What problems do you solve?
We primarily help our clients take advantage of the software that Epic has built. We’re not necessarily in the game of developing software ourselves. We work with our clients to implement and optimize the software so that they can get the most out of the Epic system.
We add the most value by bringing a product management mindset and being data-driven. We help our customers understand their operational metrics and turn the Epic complexity into operational clarity. We help them achieve the most with the software to improve those metrics and serve the members and providers that they work with.
How does your client measure the ROI of your services?
A lot of times, it depends on how we’re specifically working with them. We do a lot of implementation, so we’re the firm that customers turn to when they are going to implement the Epic payer suite. The return on investment there is focused on being on time, being on budget, and meeting the operational metrics that they have set as goals. Moving to the Epic system overall generates quite a bit of ROI, but you need to get the most out of it to realize that ROI.
We work with clients in other service lines, such as optimization or our application managed services division. AMS is focused on how we can generate cost savings by providing a managed services model in a more cost-effective manner while still delivering better quality. Then, what results can we deliver to your operational metrics?
For instance, a client that we are working with for AMS has decreased the interest and penalties they are paying by $10,000 a month. They have increased their auto adjudication rate, which is one of the most important metrics for payers and ultimately leads to significant labor cost savings.
How many of Epic’s customers use Epic’s Tapestry and Payer Platform?
About 50 organizations use Tapestry. It acts as a core administrative system for processing claims, enrollment eligibility, and medical management, such as utilization management, case management, and population health. A lot of those 50 organizations are provider-sponsored health plans.
Payer Platform focuses on interoperability between payers and health systems. That has been growing like wildfire. All of the largest commercial standalone health plans are now using Payer Platform.
Like with just about every other Epic product, Epic ultimately wins. We are seeing the large standalone health plans start to implement other components within the Epic payer suite, such as Blue Cross and Blue Shield Louisiana, as well as Humana implementing the medical management suite. Over the next couple of years, we’ll see some of these organizations take a look specifically at Tapestry and the claims processing applications too.
When you worked at Epic, how challenging was it to start working with organizations that aren’t health systems?
Most people who work in this ecosystem would have no idea that Tapestry was one of the first applications that Epic launched. They were working with a lot of staff model HMOs and provider-sponsored health plans, but obviously the core focus was on inpatient ambulatory and revenue cycle. Epic clearly established itself as the number one player in those particular markets.
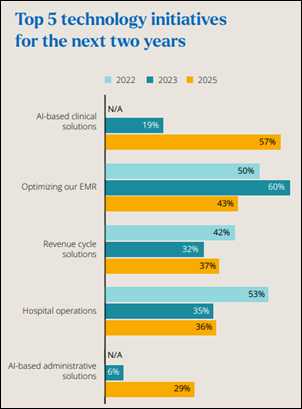
It made sense for Epic to redirect their investment into other areas outside of the traditional four walls of healthcare. That is why you’ve seen growth in areas such as life sciences, but also within the payer suite. It was exciting as the director of product management to see those dollars start being redirected to invest in the payer suite. The payer suite has essentially been number two in investment since around like 2019.
How were you were involved with Epic’s significant investment in money and headcount to implement Kaiser?
Payer suite was put on the map when we sold Tapestry to Kaiser, which had 11 million members. This was a $1 billion project overall, a little less than the $4 billion that was quoted for the health system, but parallel paths. They followed the same parallel path when the Northwest region and Oregon pushed Epic in the early days for the health system, but it was Georgia that implemented Tapestry and had real success there. That ultimately pushed the rest of the Kaiser organization to adopt it as well.
Our team had been 20 people on implementation and maybe 20 to 30 on R&D. All of a sudden, implementation was essentially 60 people and R&D grew to over 60, which could have even gone significantly higher than that just for Tapestry alone. The payer suite division grew to a couple of hundred people.
What did you learn in being an early-career employee who was put in charge of this massive project that was unlike Epic’s previous work?
An opportunity to have a career at Epic is incredible, because they take a bit of a sink-or-swim mentality. If you can survive and swim, there’s nothing like the opportunity to grow and be challenged. It’s an opportunity to rise, but it is stressful at times. We had some long weeks when we were doing the Kaiser implementation. But that completely exposed me to the industry and the ability to make an impact for Kaiser’s 11 million members. It was a phenomenal experience for sure.
What is the status of payer-provider collaboration and who benefits most from it?
I would hope that our patients, our members, and we as a society stand to benefit the most. We have over $500 billion in wasted administrative spend in healthcare year over year. We are called Canopii Collaborative because we truly believe that the only way that we can reduce that wasted administrative spend is by focusing on helping payers and providers collaborate to seek opportunities where we can do better data exchange, reduce unnecessary exams and tests, and change the model by how we pay and finance healthcare in moving from fee-for-service to value-based care to ultimately reduce that administrative spend.
We at Canopii established ourselves as the primary firm that you should turn to for the Epic payer suite. To start to bridge that payer and provider collaboration, we acquired Anchor Healthcare Consultants, which focused on revenue cycle. We are continuing to focus on that area.
Between CMS-0057-F and other regulation around interoperability and payer-provider collaboration, I have a lot of hope. I also have a lot of hope that AI will help accelerate this initiative and get us there faster. It is fundamental to reducing the total cost of care in this nation, which is frankly unsustainable.
How did your background prepare you to run companies?
I’ve been an entrepreneur ever since I was a kid. This is probably like my seventh company, but the first one that is truly successful.
My experience at Epic prepared me for leading a company like this. Epic still operates as fairly entrepreneurial. It’s very flat, and they place a lot of trust in those individuals who are essentially leading divisions like I did for the Tapestry team. That definitely prepared me, but it’s very different when you also have to handle all the backend function functions like finance, HR, and operations without the support of those great teams like they have at Epic.
It has been a fun ride, for sure. We were excited to be named the 67th fastest growing company on the Inc. 5000 last year. I’ve read that magazine since I was in middle school and an aspiring entrepreneur, so that was a pretty big milestone for us. We are excited about the growth to come.
How did you meet the challenge that faces most companies, but especially consulting firms, to create and maintain a culture?
It is cool to see team members who come over to Canopii who have typically worked at other consulting firms. The comments that they share with us are exciting. What makes the biggest difference is that we treat them as people and not just another number. Perhaps most importantly, they enjoy that we actually understand what they are doing day-in and day-out.
I previously worked at Epic. Our other co-founder was at Epic as well, and then worked as a consultant for a few years. We have maintained a culture where we understand what it is that you do day-in and day-out. We are here to support you. People have gotten into the mission and then the ecosystem that we have created. If you are struggling with an issue, you aren’t sitting on a deserted island. You can come and work with all of the other 60-plus experts that we have in the Epic payer suite to identify someone who has had a similar issue, then work together to bring that back to your client and add value.
What is the company’s strategy over the next few years?
A big focus for us will be expanding our application managed services team. We’ve seen a trend towards managed services over the last couple of years, I fundamentally believe that AI will accelerate that trend. We are focused on working with our clients there, because when we have the opportunity to support them end to end, we can make a significant difference. We are seeing the turnaround on some of not only the IT metrics, but more importantly, the operational metrics that we’ve been working on with our first AMS client. That will be a real focus for us over the next couple of years.
Healthcare in this country is, unfortunately, systemically and fundamentally broken. No single individual or single branch of government can turn that around. It can be overwhelming, particularly at the macro level.
I encourage our customers, other vendors, and our team to adopt the Boy Scout model and leave it better than you found it. Identify the particular area where you can make an impact. Even if you are just one analyst at one client, you can make an impact. Or you may be the CEO of a vendor that is seeking to make a difference between payer and provider collaboration.
Everyone can ultimately contribute to making those small impacts. Then, in aggregate, hopefully we can start to move healthcare towards a model that’s more sustainable for us as a country.
Comments Off on HIStalk Interviews Brent Benner, President, Canopii Collaborative




























I haven’t been to Bostain in decades so I’m having who’s-on-first problems here. Is Deaconess who they’re merging with? So…